Does your child spend too much time on the phone? And you wonder why your kid behaved abnormally recently? They might be texting someone they shouldn’t. Stop guessing! The only thing that you must do is learn how to hack someone’s phone without touching it. You might wonder is it even remotely possible to do this? Keep on reading this post to remove your worries thoroughly. We won’t tell you to monitor your child 24 hours per day. You have to work, to be busy doing your own staff. Actually, it has now become easier to hack a phone or access its activity remotely by using a remote cell phone monitoring app. You can track any device without physically accessing it all the time.

A couple of years ago, this may sound odd but not now. The spying tools below are mostly used by concerned individuals who would like to track their loved ones and protect them from an unforeseen situation. In this post, we will make you familiar with three best apps that you should try. So, if you have interest in finding out how this can be done, read on!
Some Reasons Why People Hack Others Phones
You may be thinking that hacking someone’s phone is done to perpetuate evil but that is not necessarily the case. Many genuine person with genuine problems want to monitor and know what is going on around them. As we all know in this digital age, information is power. So it may become necessary to know what the people around you are up to. There could be plenty of reasons for using a remote cell phone monitoring app. From employers to parents, everyone can take the assistance of these tools.
- Parents hack the phones of their children to monitor their movements and to prevent them from being misled by damaging and obnoxious contents.
- Others want to know whether they are cheated.
- Employers also hack their employees phones to ensure they aren’t passing on company secrets. Information or data is a valuable resource hence you need to safeguard it by monitoring those who have knowledge of the information so as to prevent them from leaking your secrets.
- Governments of every country also hack their citizen’s phones to make sure they are planning against them.
Monitoring apps indeed help parents, spouses, employers remove some worries instantly. Besides, you can consider install a monitoring app on your own phone in case it is stolen one day. Take the assistance of these remarkable tools right away and track someone else’s device remotely.
1. Track A Xiaomi Phone with mSpy
mSpy is one of popular monitoring apps which can be used to track a smartphone. mSpy collects data from the device and displays it in the Control Panel which you can access from any browser.

To start using mSpy, you need to check the compatibility of the device you’d like to monitor, choose the subscription plan and proceed with the purchase. After that you receive an email with the login and password to your personal Control Panel. Log in to your Panel to find the installation instructions. To install the mSpy app you’ll need to have a full authorized physical access to the target device. Launch the target mobile phone’s browser, type in the link for downloading the mSpy app and continue with the installation. By installing mSpy, you confirm your intention to use this software legally. It has an interactive dashboard as well that can be accessed from any device. Although you might have to root or jailbreak the device to make it work.
- It tracks the real-time location of the device.
- All the data can be accessed remotely.
- Excellent 24/7 customer service with multi-language support.
2. Track A Xiaomi Phone with PanSpy
 Undoubtedly PanSpy can satisfy all your needs as one of the best mobile monitoring apps. You can access location, contacts, messages, browser history, call logs, and so much more important data remotely. You are able to choose keep its app icon or remove it on the target device. It compatible with all the popular mobile devices. PanSpy is easy to set up on target device without keeping any of your personal data. And they own more powerful features compared with rivals and offer free technical support. PanSpy is dedicated to developing an exclusive product of the finest quality and pursuing excellence in every aspect, they offer professional service for many countries and outstand in the field of monitoring tool.
Undoubtedly PanSpy can satisfy all your needs as one of the best mobile monitoring apps. You can access location, contacts, messages, browser history, call logs, and so much more important data remotely. You are able to choose keep its app icon or remove it on the target device. It compatible with all the popular mobile devices. PanSpy is easy to set up on target device without keeping any of your personal data. And they own more powerful features compared with rivals and offer free technical support. PanSpy is dedicated to developing an exclusive product of the finest quality and pursuing excellence in every aspect, they offer professional service for many countries and outstand in the field of monitoring tool.
Remote Monitoring in 3 Easy Steps
Step 1: Simply register a PanSpy account on their site. Complete the steps and check your email for the installation instructions. First of all, you have to open a web browser and visit PanSpy official website. Click on the Sign up button to create a PanSpy account. Create PanSpy Account
Step 2: Select Android System. Get physical access to the target device and visit www.panspy.com to download PanSpy Android app. Go to the settings of target Xiaomi device and authorize PanSpy following the instructions. Install the app and launch. Choose to keep or remove the app icon after installation.
Step 3: Install PanSpy App on Xiaomi Phone. After successfully subscribed the service, you will get a download link, simply download and setup the PanSpy app. Login in with your PanSpy account and authorize PanSpy according to the instructions. You can choose to keep or remove the app icon.
Step 4: Remotely Check Data on Huawei Phone. Now, enter PanSpy login details that you have created in step 1 and accept the permissions to start monitoring. Switch back to your computer or your own phone and open PanSpy online dashboard in any browser to remotely hack the target Xiaomi phone.
3. Track A Xiaomi Phone with Spyzie
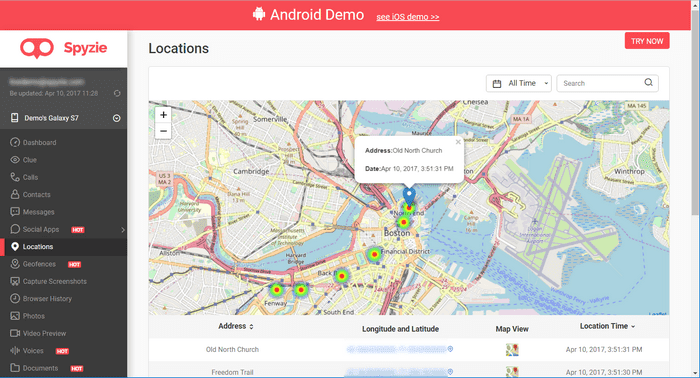
You can use Spyzie to access all the vital information related to a device. Compatible with most of mobile devices. Since it runs in a stealth mode, the targeted user is not able to detect the presence of the apps as well. Spyzie is used by countless parents globally to track their child’s cell phones. It is easy to set up and use. Even employers use Spyzie to make sure that their staff are actually working on the job at hand. In addition all of this Spyzie guaranteed that there is no chance of your data being stolen with Spyzie’s world class encryption, no one can find out you are monitoring their phone.
- It has a web-based dashboard (and mobile app) that users can access remotely.
- Tracks the device’s all the important data
- Runs in a stealth mode
 Remote Monitoring in 3 Easy Steps
Remote Monitoring in 3 Easy Steps
- Sign Up: Create a free Spyzie account with your email.
- Configure Spyzie: Spyzie’s setup wizard will guide you through the configuration process.
- Start Monitoring: Access Spyzie’s dashboard and view all their data.
How To Remove A Hacker From My Phone
For most of us, our smartphones play a crucial role in our lives. From it, we are able to connect instantly with our friends and loved ones, make appointments, book a flight, make reservations and do a whole lot of things that was Impossible to do a couple of years ago. With the changing tides that herald the arrival of technology, it is now far easier for us to do more and be more but it comes at a cost.
How To Hack Into Someone’s Phone Without Touching It
Our smartphones are digital storages or safe-boxes for everything related to our lives. It is no wonder that the issue of privacy is a much-discussed topic in our media today. Every now and then, there is a data breach in which confidential and personal messages and data are taken without the consent of their owner. Even though this in a way helps in exposing major misconduct by public officials, most of the time they dedicated to really hurt someone. Cybercriminals hack into unsuspecting phone users and steal their information to commit crime.
How Do You Know If Your Phone Has Been Hacked?
Most of the time, smartphone users do not take notice of their phone’s privacy health until it is way too late. But one of the best give away is when your phone all of a sudden gets sluggish. Another way is when your smartphone’s battery easily drains without you really using it. Although this may be the phone telling you that you need to upgrade the operating system, you need to properly investigate to make sure no malware is stealing your data and draining your battery alongside.
Who Could Be Responsible For This?
Anyone could have done this. But before you go around shaking every cage, you need to know that it may not be anyone around you. It may be a cybercriminal who is just randomly gathering data.




Hacker hire spyhackpro9 on googlemail